Introduction and Networking Primer
Driven by the lack of clear information I had when I started, I wanted to write something about Nmap, try to present the options in as structured a way as possible and provide some insight and detail instead of just “instruction”
I am sure that there are better tutorials out there and this is as much an aide-memoire for me as it is a tutorial for anyone else. Also, I don’t intend to re-invent the wheel here so I will quote from sources that have already explained subjects and I will reference those source by indexing notes using bracketed numbers e.g. [999] and a bibliography
What is Nmap
The offical Nmap book introduces Nmap as:
“…a free and open source utility for network exploration and security auditing…”[1]
In its simplest form it is an advanced IP Scanner, much like the windows utility of the same name and others you may know such as Angry IP Scanner. In its more advanced form it is so much more with a scripting engine that allows anyone to extend the capabilities through its own language, NSE
I hope to write something about NSE in a future post, but this first part is a basic introduction. The intention is to show you what can be done with fairly simple commands, I’ll also try and demonstrate what you might see as a defender using Wireshark captures and some small videos.
In order to understand the material you will need a basic grasp of TCP/IP networking and protocols, and this primer starts with that. If you are comfortable with the basic principles of using Ping and the TCP handshake, feel free to skip forward.
ICMP
ICMP – Internet Control Message Protocol ICMP can be descibed as:
“…a supporting protocol in the Internet protocol suite. It is used by network devices, including routers, to send error messages and operational information indicating success or failure when communicating with another IP address, for example, an error is indicated when a requested service is not available or that a host or router could not be reached.[2]”
Most IT folk and network engineers will recognise ICMP as the protocol used by tools such as Ping and Traceroute (tracrt on Windows).
Using Ping to find a host and see if it is up and responding normally you send a command similar to this
Ping 192.168.33.16This behaves a little differently in windows than in other operating systems. In windows it sends only four requests and then terminates, in other operating systems such as Linux and MacOS, it is continuous until you terminate it. You can see in the video that I terminate this using CTRL-C.
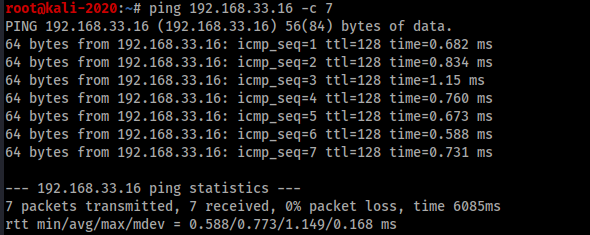
As an alternitive you can use the -c switch and given the command a count of requests to send
Ping 192.168.33.16 -c 7a Ping contains two parts, a request and a reply. In our terminal what we see are the replies:
So what is happening on the endpoint being tested?
Using Wireshark we can see traffic coming through various network interfaces on an endpoint. I won’t cover the use of Wireshark in this post, I may do a separate one at some point, but this is what we see
you can clearly see seven requests and seven replies in wireshark and in the terminal we are told that seven were sent and seven received.
TCP/IP
So having talked briefly about ICMP and its most common use, lets discuss somethign a bit different.
ICMP sends a request and the endpoint may receieve the information, it may not. Similarly for the reply, the endpoint sends the reply, but ha sno knowledge as to whjether or not it is received. This doesnt really work well for more sensitive communications.
If you want to share some information with someone in your office, just randomly talking to them without having them acknowledge they can here you or even realise you are talking to them is not the best way to get information to them. You wouldn’t start talking to them until they were ready, you’d check they could hear you and probably check they had gotten all the information at the end of the conversation.
So we need a better method to share information, one that starts with a “are you ready” and ends with “that’s all folks” the common method in networks today is a thing called TCP
I don’t intend this to be an in depth discussion or tutorial on TCP and how it works other than to demonstrate with a simple, primer the bits particularly of interest in connection with Nmap.
TCP is a connection-oreinted protocol, which means that a connection is established and maintained until the conversation is finished and both ends acknowledge this. During the conversation it may break up that data into smaller peices and send them in a random order, but in a way that allows them to be reassembled in the correct order and in way that means the recipent knows if there are any peices missing.
As we would not start our conversation without makign sure out recipient was listenign and could hear us, so TCP doesnt start until it has compledt that step, we call this the “TCP Three Way Handshake.”
Step 1 Before starting to talk we need to know the intended target is listening, we do ths by sending a peice of data we call a SYN packet, think of it as asking the target to start a conversation with you. So that each concurrent conversation can be tracked, the computers uses a random sequence number
Step 2 If the target computer receives you request to start a conversation (SYN) then it reposnds with an acknowledgement. Its called a SYN-ACK and it contains a sequence number that is one higher than that in the original SYN request along with its own sequence number so it can keep track of its own conversations.
Step 3 So having asled you colleague if they have the time to chat and they ahve said yes, before starting you might acknowledge them and say something like “Good, Ok, so…”
The computer is much more succint and simply sends its acknoiwledgement as an ACK
So we have sent a SYN SYN-ACK ACK this is the TCP Three Way Handshake.
You can see this handshake in wireshark, this image shows a wireshark capture that has that handsahke as the first three packets
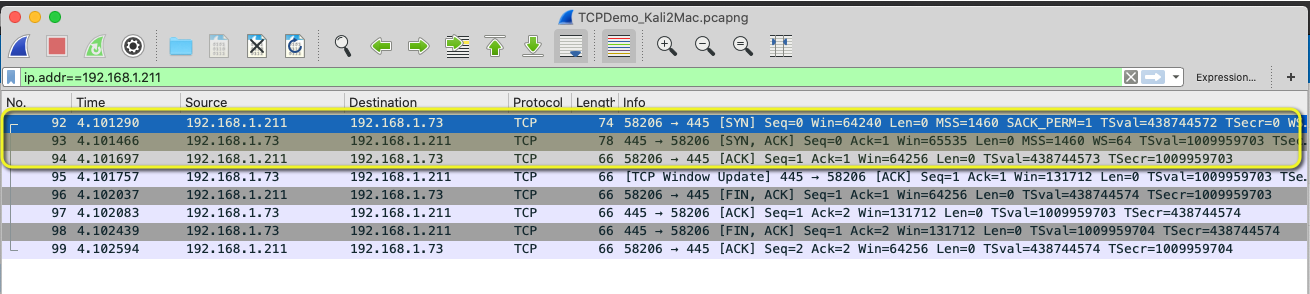
Of course, sometimes you may ask somebody if they have time to talk, and then your phone rings, or some other event means that you can’t continue, you’d acknowledge this by apologising and ending your attempt to exchange information and as you would expect TCP can do this as well
The computer might send a SYN asking to start a conversation but the user ends the application and so that connection can be ended by sending its own reset this is known as RST…
And finally…
In the same way you would end the conversation or information exchange with you colleague, computers using TCP tell the recipient that it has finished sending data, the recipient acknowledges that it has received everything and understands there is no more to come and they agree to close the connection.
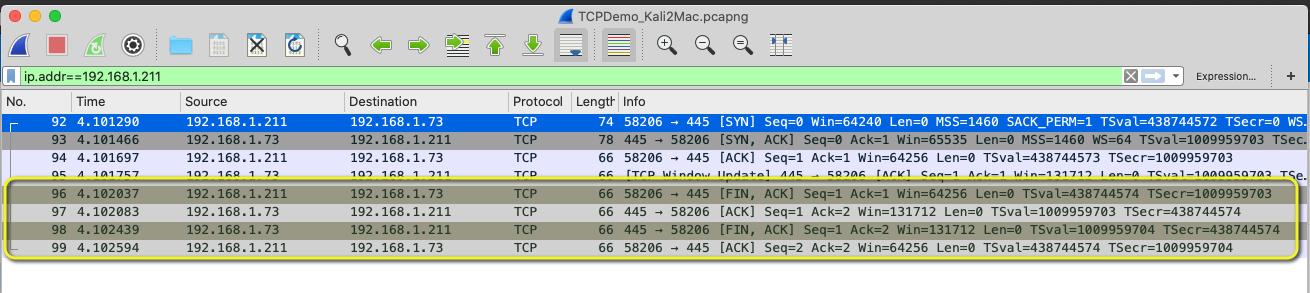
as we started the conversation with a three way handshake we end it the same way, but this time using something know as FIN packet
The theory says the same method is used and that we should see FIN, FIN/ACK, ACK, but as you see in this image, we don’t, instead we see that the source sends FIN/ACK, the target responds with an ACK and then the Target sends FIN/ACK and the sources sends ACK
In this alternative capture we see a different set of packets, the source sends FIN/ACK and the target sends ACK. The target then closes the socket with an RST packet

Bibliography
[1] NMAP NETWORK SCANNING – Gordon “Fyodor” Lyon – Published by Insecure.com LLC ISBN 978-0-9799587-1-7
[2] https://en.wikipedia.org/wiki/Internet_Control_Message_Protocol