This was the first box I pwned in anyway and to be fair it was very straight forward and done entirely by guesswork from my “knowledge” of common windows exploits, there was no clever methodology just a moment when I thought “Oh! Its windows XP lets try….”
So lets try and walk through the steps in a semi structured way. Of course we start with reconnaissance using Nmap
nmap -A -T4 10.10.10.4
This brought its usual output… lets have a look at it in a bit more detail
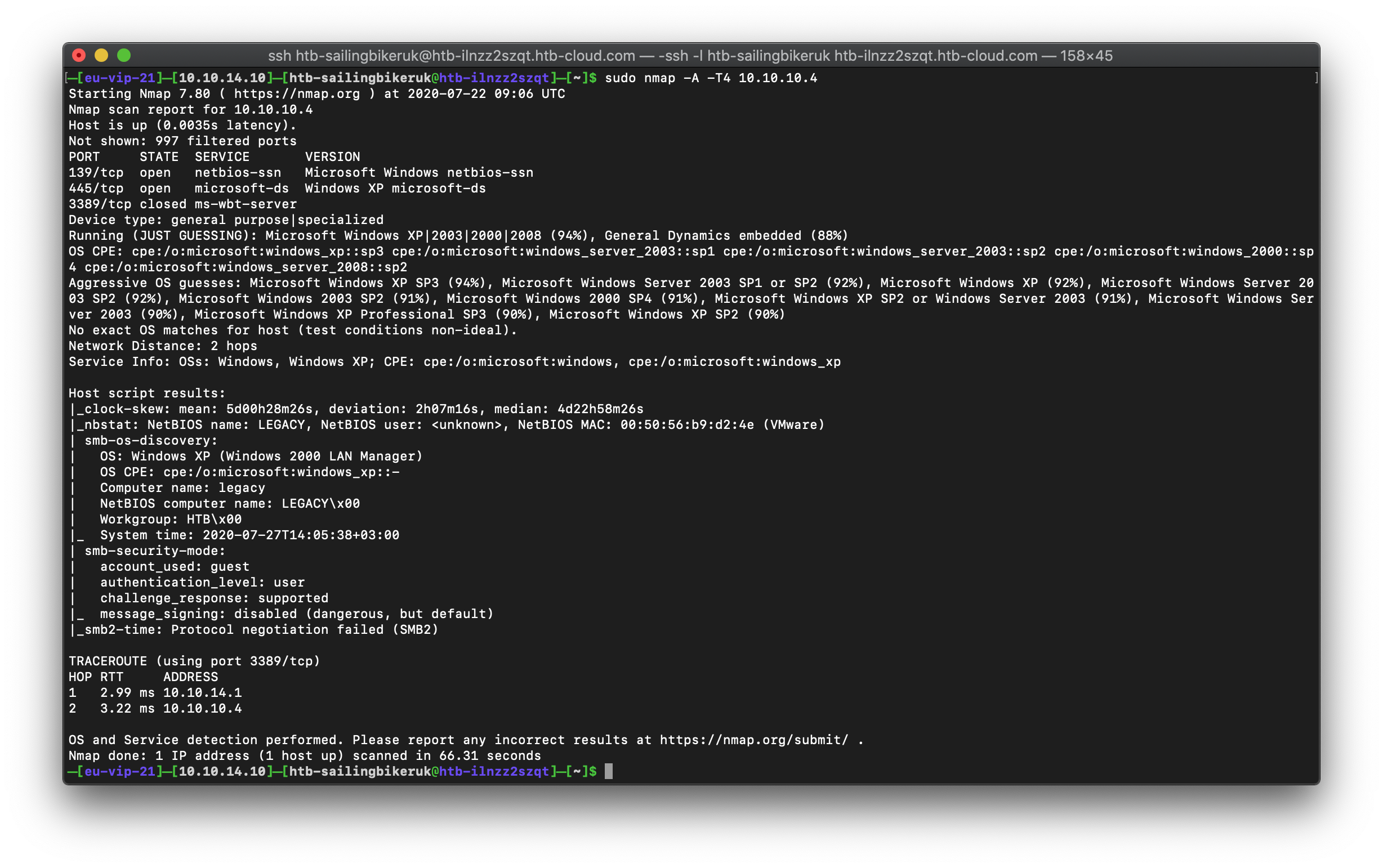
What do we have listed?
Port 139 and 445 which we know are SMB and port 3389 which is RDP.
We can try and enumerate SMB and we could try and attack RDP – it certainly has had a few vulnerabilities recently
Enumerating SMB didnt work

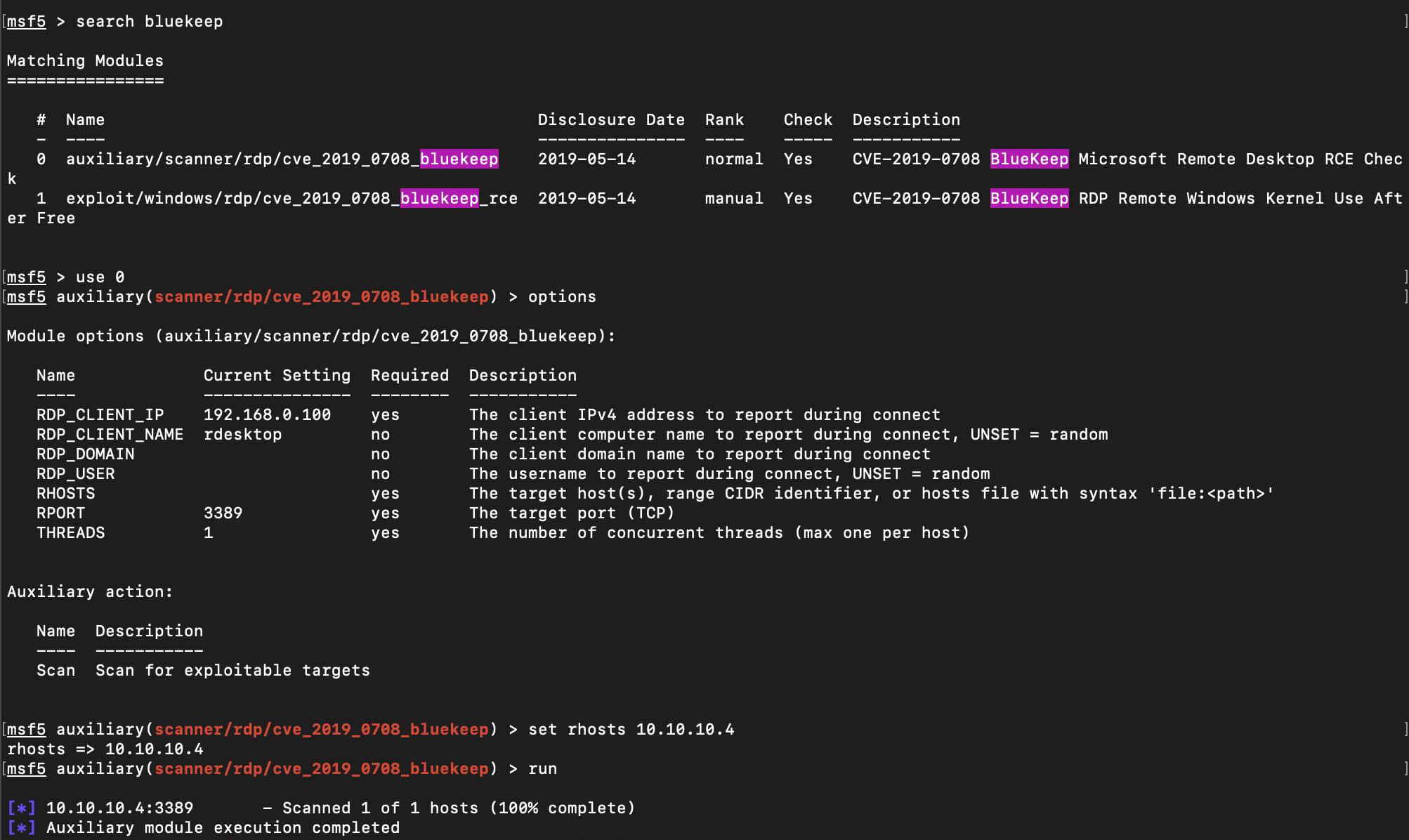
Lets have a go at RDP – Bluekeep (CVE-2019-0708) is the most recent, well publicised vulnerability so lets try that. Fire up msfconsole and lets see if we can find an exploit for it.
msfconsole search bluekeep
It looks like there is a scanner which tells us if the system is vulnerable lets run that first

Hopefully you know that to use a particular module in metasploit you need to tell it which one to use. You can do that by copying the full path to the exploit or by using the number next to it in the search results, both of the commands below bring the same result.
use 0 use /auxilliary/scanner/rdp/cve_2019_0708_bluekeep
Running the scanner brings back no results and suggests it isn’t vulnerable, go ahead and run the exploit if you like to see what happens but it didn’t succeed for me.
So what next? We’ve been unsuccessful against both protocols that are showing with the obvious checks…. this is where I had my “Oh! Its windows XP lets try….” moment.
The first exploit I was shown and that I ever had success with was MS08-067. It was also a critical vulnerability in the first proper pen test we did at work with huge numbers of vulnerable machines. It was so bad they stopped the test and called us in to discuss. We fixed it over the next 24 hours and it was the catalyst for a centralised Vulnerability Management program in that business, it has always stuck with me but in this instance it was just a guess on my part. It was something to try blindly. this is what I did.
In Metasploit search for MS08-067, select option 0, set the options and run the exploit. It connects, returns a metepreter session and you are running as SYSTEM.
